

With the development of IT-technologies, cyber-attacks appear all over the news, and bring anxiety to the business owners. But don’t you worry, we’ve got your back covered.
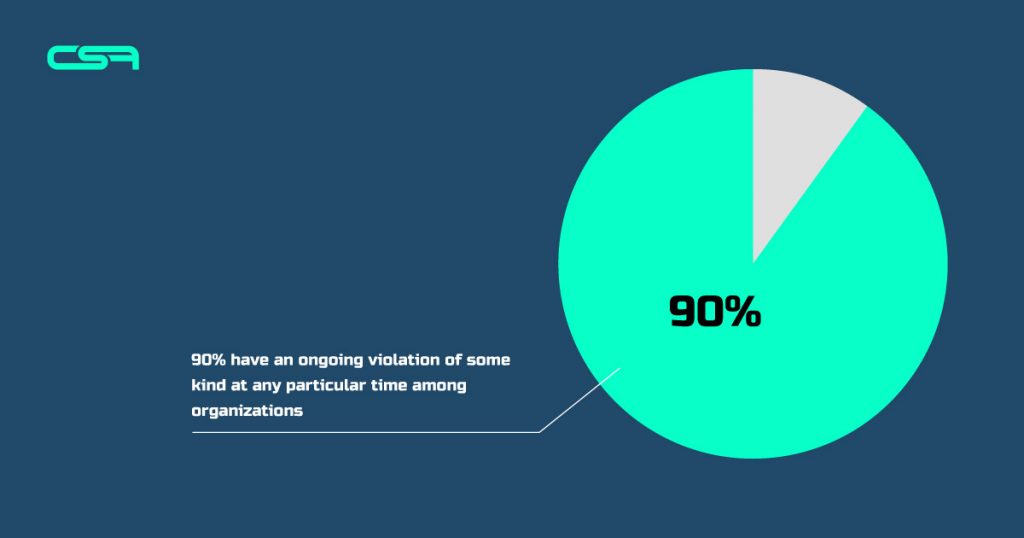
Surprisingly, most businesses still follow the old, only partially efficient ways of safeguarding their confidential data, primarily with technologies intended to prevent future attacks. But it is almost impossible these days to potentially avoid bad guys from sneaking into corporate networks and trying to get their hands on confidential data. In reality, over 90% have an ongoing violation of some kind at any particular time among organizations. Moreover, it might not even be identified by those organizations.
Rather than only concentrating on stopping the initial wave of the attack, all these indicators lead to the need for effective breach detection to provide a “last line of defense” against these threats.
A breach detection system is a perfect blend of safety measures and apps developed to target infected devices, malware, and other vulnerabilities that occur within your network. It serves to maintain the persistent barrage of hackers at bay by having a data breach detection system in place. However, for a concrete plan, you should incorporate this defensive strategy with extra offensive methods (like internal and external honeypots).

The definition of a Breach Detection System (BDS) is very similar to an antivirus. That’s true, however, an antivirus program tests for known malware on a single device, but a BDS observes activity on an entire network.
In order to safeguard against the multitude of emerging attacks, particularly unidentified malware, IT companies use BDS. With exception of tier 1 security that scans traffic flows, such as a firewall or intrusion prevention, BDS focuses on malicious activity within the network it serves to protect. Various sets of heuristics, traffic analysis, risk assessment, secure marked traffic, data policy understanding, and reporting of violations determine possible breaches. Using these techniques, BDS can sometimes find breaches as they arise and identify violations and side-channel attacks that were not initially found on other occasions.
The contemporary cyberattacks are intended to bypass the classic defense measures of your business (regardless of your size or industry). It requires companies an average of 99 days to identify a violation, as per the Mandiant-Trends Report of 2016. Whereas, it only takes about three days for hackers to obtain admin privileges and impose damage once they breach a system.
The traditional ways to detect violations just aren’t enough because, on their own, they are unable to provide the appropriate security you need.
BDS’s identified security threats are a little broader in action when compared to what is found by a conventional anti-malware device. The malicious software the BDS is searching for may be part of an aggressive software suite, manually operated by an attacker.
Every specific program run may seem consistent with the company’s regular activities. It could be the implementation of legitimate software on your device that already resides. BDS not only looks at each individual operation but recognizes variations of programs for malicious purposes that can be mixed.
BreachSight is UpGuard’s highly professional data breach system, which offers a variety of protection items that are suitable for online retailers.
There is an enticing control console for the BreachSight device that is available online. The entire program is on the cloud, so you don’t need to think about the cybersecurity system’s host server room.
Data safety is approached from two angles by the security system:
The vulnerability scanner continually operates. It warns of any suspicious data access efforts to the data manager. It will also show flaws in device protection that need to be shut off. The scanner searches for damaging processes to run and checks the program code, identifying for malicious intent.
Trend Micro is a top brand of antivirus products. In order to offer more robust cybersecurity facilities, all AV vendors are currently moving forward. Trend Micro has provided a violation detection system to sprint ahead of the competition – Deep Discovery Inspector.
This is an appliance, just like a firewall, that you plug into your network. Do not substitute your boundary security services with the Deep Discovery Inspector because the attention of this system is drawn to network operation.
This tool’s advantage is its ability to capture Trojan software’s interactions with its external controllers.
A very distinctive characteristic of threats that are meant to block breach detection systems is that apparently unrelated software is exploited for malicious purposes to function in concert. The goal of Deep Discovery Inspector is to identify the driving power commanding legitimate applications to lead to data breaches.
Fortinet specializes in network security against Internet-bound threats that are incoming. FortiSandbox is accessible as an installation, as a virtual machine running on-site applications, or as a cloud-based subscription service.
Breach detection systems begin with the assumption that it is possible to defeat network access security. The strategy of FortiSandbox includes separating new software and tracking its response to the network’s resources and services. This is a lockdown approach that enables the program to run entirely. But to allow complete device rollback, it sets savepoints. From firewalls and gateways to endpoints, FortiSandbox communicates with all levels of your networks.
Every day, data security becomes increasingly more demanding. To avoid data leakage or device breaches, you can’t rely exclusively on a firewall and conventional antivirus. To feel safe, breach detection systems implementation is a must.
Hackers know how to manipulate workers into giving away their login details these days, so it is not enough to just look at external access to your system to secure the data stores of your business. You need more advanced tools for data security, such as a monitoring system for breaches. Contact our team to get help with making your business secure.