

According to the Newrix research, together, DoS and DDoS attacks are the most common types of cyberattacks. Such cybercrime cases continue with significant speed. Nexus Gard statistics prove it. They say that in Q1 2020, there was a whopping 542% increase in DDoS activity compared to Q4 2019. What makes it one of the most popular types of cybercrime? The reason behind it is the unbelievable simplicity of such a severe attack. Without a quick solution, it may kill the reputation of the company, dispose of potential customers, reduce website search console ranking, and much more.
But how? What are the DDoS attack consequences? Just imagine a situation when you follow the link to the website and see nothing. No available website, just an error. What do you think at that moment? Will you return to such a website? Will you trust the web site’s owner, services or products, and the company’s security? Will you recommend it?
We are sure that the answers are “No”. You will find another service or company, especially if you need a quick solution to your query. That is why it is so important for a successful businessman to know how to stop a DDoS attack before it leads to any kind of loss.
To help you with this we have prepared this article reading which will let you know:
DDoS (distributed denial-of-service) attack is a malicious attempt to break down an online service, host machine, or network. Moreover, it can thwart access for users to almost everything: servers, devices, services, networks, applications, and much more.
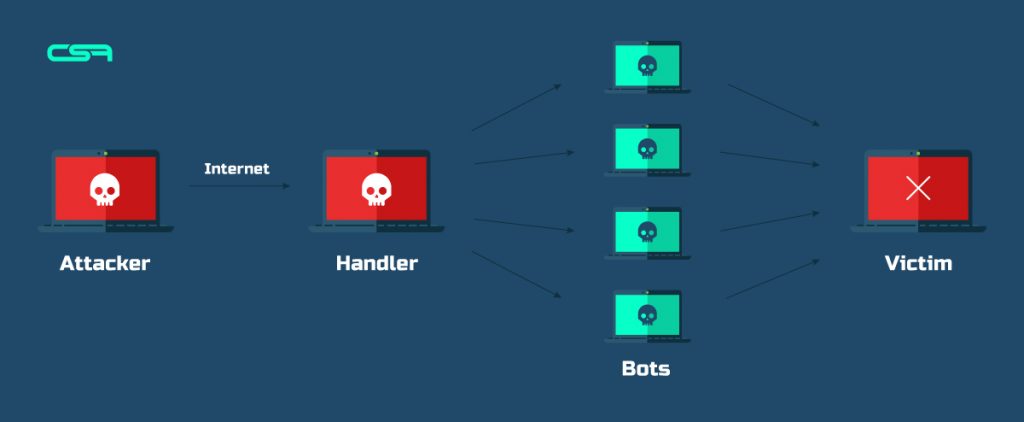
To execute DDoS attacks hackers use a system of bots that are curated by the Handler bot pointing at the victim server. Usually, they send a bunch of requests and leave them unanswered. This way the server gets overloaded and shuts down.
You can either see how it works in the following image :
Rising of cybercrime extends the boundaries of all hacking types, including DDoS. A lot of sources write about 10, 20, and even 30 DDoS types. But there are 3 common types that are really known and used more often.
A volumetric attack is the classic type of DDoS attack. Its main goal is to not let the traffic come to. In order to implement this, hackers start to push lots of requests (using bots) that clog up traffic and overload the server making it inaccessible for other users.
Protocol attack focuses on the damages with the processing capacity of network infrastructure resources like servers, firewalls. Hacker tasks bots to target Layers 3 (network layer) and 4 (transport layer) of protocol communications with malignant inquiries.
Application DDoS attacks are more refined attacks that apply by really skilled hackers. This attack-type uses weakness points in Layer 7 (application layer). It’s trying to open connections and initiating processes and transaction requests that consume finite resources like disk space and available memory.
Of course, identifying and preventing attacks early is the best practice to save yourself from such cases. There are some tips how you can do it:

If you have a big bandwidth available to your Web server it may give you a few extra minutes to act before your resource will be overwhelmed. Yes, it can’t save you from attacks but it gives time and you can accommodate the sudden and unexpected surges in traffic that, for example, are not attacks.
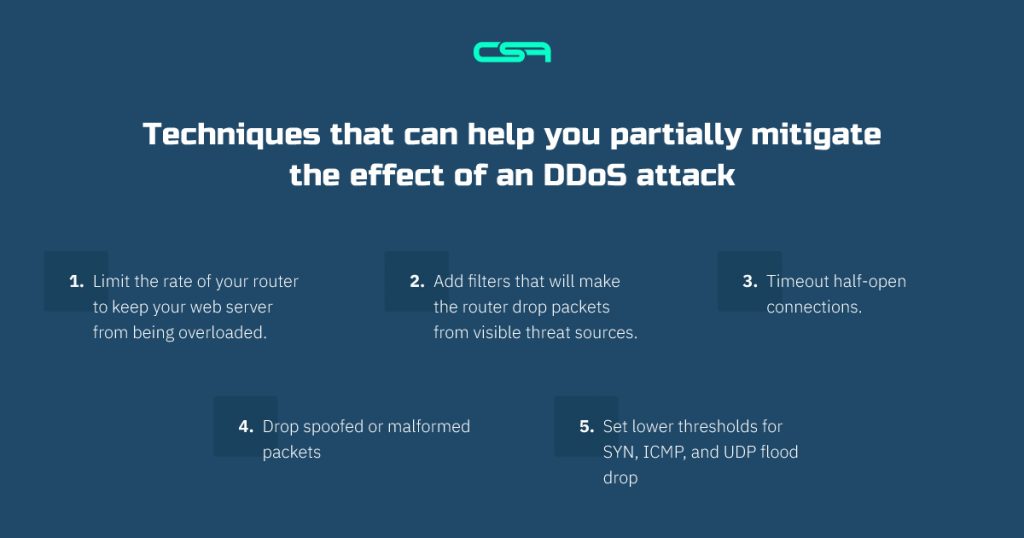
If you have your own Web Server you may try to defend at the network perimeter. There are some techniques that can help you partially mitigate the effect of an attack:
So, if you are already attacked and you implemented everything mentioned before, the next step is to call your hosting provider. You need to tell him what’s happening, but by that time he may already know it or they may themselves start to be overwhelmed by the attack. It can help you because its data center will likely have far higher bandwidth links and higher capacity routers than your company has, and its staff will probably have more experience dealing with attacks. If they are powerless you should implement the next solution.
If you are the owner of an enterprise or big organization you definitely should have a number of mitigation services that will respond quickly. But if not, look for them as soon as you know that you are attacked. These companies have the vast infrastructure and use a range of tools, including data scrubbing, to help keep the website up. Moreover, you can make a longer-term contract with providers for arranging mitigation for such attacks. Some of these contracts even consist of emergency coverage offers.
Conclusion
As we already said, this problem is hard to save and it’s better to make everything to prevent this. The best solution that will always work – is cooperating with a cybersecurity company that will respond quickly and can grant you emergency coverage. It’s hard to choose one in such a sophisticated market, but we specialize in finding the best match for you, just contact us.